A new threat actor called Amaranth Dragon, linked to APT41 state-sponsored Chinese operations, exploited the CVE-2025-8088 vulnerability in WinRAR in espionage attacks on government and law enforcement agencies.
The hackers combined legitimate tools with the custom Amaranth Loader to deliver encrypted payloads from command-and-control (C2) servers behind Cloudflare infrastructure, for more accurate targeting and increased stealth.
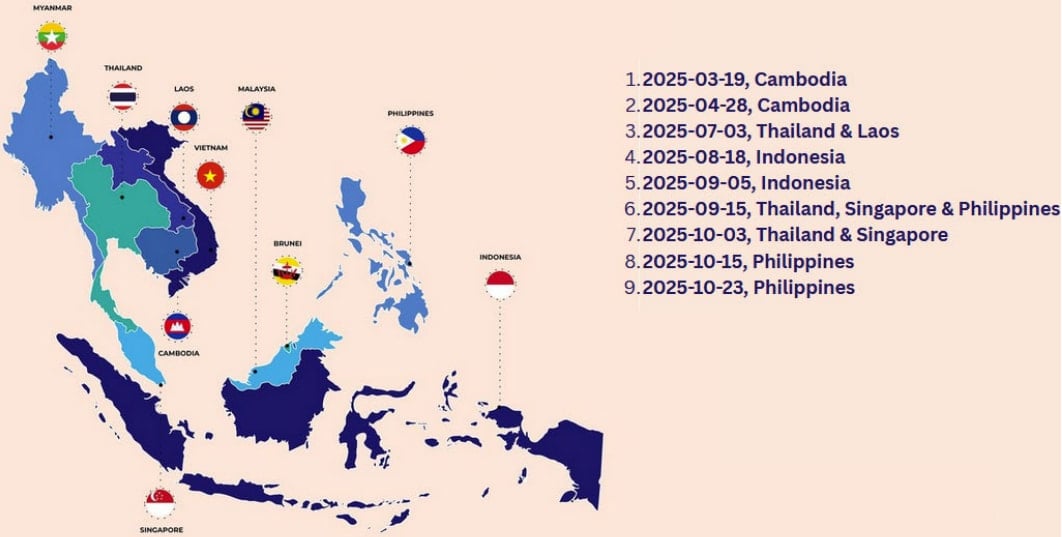
According to researchers at cybersecurity company Check Point, Amaranth Dragon targeted organizations in Singapore, Thailand, Indonesia, Cambodia, Laos, and the Philippines.

The CVE-2025-8088 vulnerability can be exploited to write malicious files to arbitrary locations by leveraging the Alternate Data Streams (ADS) feature in Windows. Multiple threat actors exploited it in zero-day attacks since mid-2025 to achieve persistence by dropping malware in the Windows Startup folder.
Last week, a report from Google Threat Intelligence Group (GTIG) showed that CVE-2025-8088 was still actively exploited by multiple threat groups, including RomCom, APT44, Turla, and various China-linked bad actors.
Check Point reports that Amaranth Dragon started exploiting the WinRAR flaw on August 18, 2025, four days after the first working exploit became publicly available.
However, the researchers have been tracking the malicious actor’s activity since March 2025 and identified multiple campaigns, each restricted to targeting one or two countries via strict geofencing.
Furthermore, the lures used in the attacks were themed around geopolitical or local events.
In attacks before August 2025, Amaranth Dragon’s attacks relied on ZIP archives with .LNK and .BAT files that included the scripts to decrypt and run the group’s loader.
When exploits for CVE-2025-8088 became available, the threat actor leveraged the vulnerability to place a malicious script in the Startup folder. In some cases, a Registry Run key was also created for redundancy.
These mechanisms launch a digitally signed executable that launches the Amaranth Loader payload using the DLL-sideloading technique.
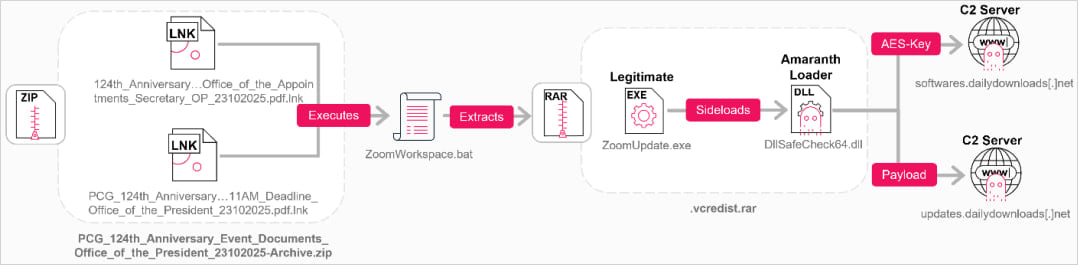
The loader retrieves an AES-encrypted payload from an external URL and decrypts it in memory. In many cases, this payload was the Havoc C2 post-exploitation framework, which has been abused in cyberattacks since at least 2023 and also seen in ClickFix-based attacks.
To filter traffic from countries outside the attack scope, the actor used C2 servers behind Cloudflare infrastructure configured to accept traffic only from targeted regions.
Check Point observed a new remote access tool, tracked as TGAmaranth RAT, being deployed in more recent Amaranth Dragon attacks. The RAT uses a Telegram bot for C2 activity.
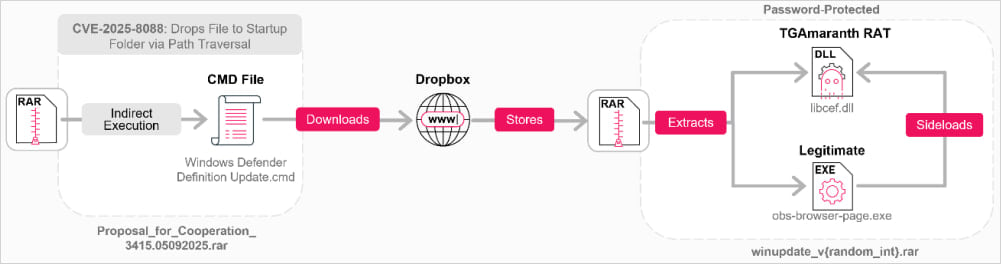
TGAmaranth also supports file uploading/downloading, taking screenshots, and listing running processes on the host.
It can evade detection by implementing various protections against debugging, antivirus, and endpoint detection and response (EDR) solutions, which include replacing a hooked ntdll.dll, a Windows system library used for low-level interactions, with an unhooked copy.
Given the widespread exploitation of CVE-2025-8088 by multiple threat actors, organizations are advised to upgrade to WinRAR version 7.13 or later (the latest is 7.20), which addresses the flaw.
Check Point says that Amaranth Dragon’s attacks show that the actor has “technical proficiency and operational discipline” and can adapt its tactics and infrastructure for maximum impact on its targets.
The researcher’s report contains indicators of compromise for archives, URLs, supporting files, and the malware used in attacks. YARA rules are also available to help defenders detect Amaranth Dragon intrusions.

Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of tools you already use.














