A subgroup of the Russian state-sponsored hacking group APT44, also known as ‘Seashell Blizzard’ and ‘Sandworm’, has been targeting critical organizations and governments in a multi-year campaign dubbed ‘BadPilot.’
The threat actor has been active since at least 2021 and is also responsible for breaching networks of organizations in energy, oil and gas, telecommunications, shipping, and arms manufacturing sectors.
Microsoft’s Threat Intelligence team says that the actor is dedicated to achieving initial access to target systems, establishing persistence, and maintaining presence to allow other APT44 subgroups with post-compromise expertise to take over.
“We have also observed the initial access subgroup to pursue access to an organization prior to a Seashell Blizzard-linked destructive attack,” reads a Microsoft report shared with BleepingComputer.
Microsoft’s assessment is “that Seashell Blizzard uses this initial access subgroup to horizontally scale their operations as new exploits are acquired and to sustain persistent access to current and future sectors of interest to Russia.”
Targeting scope
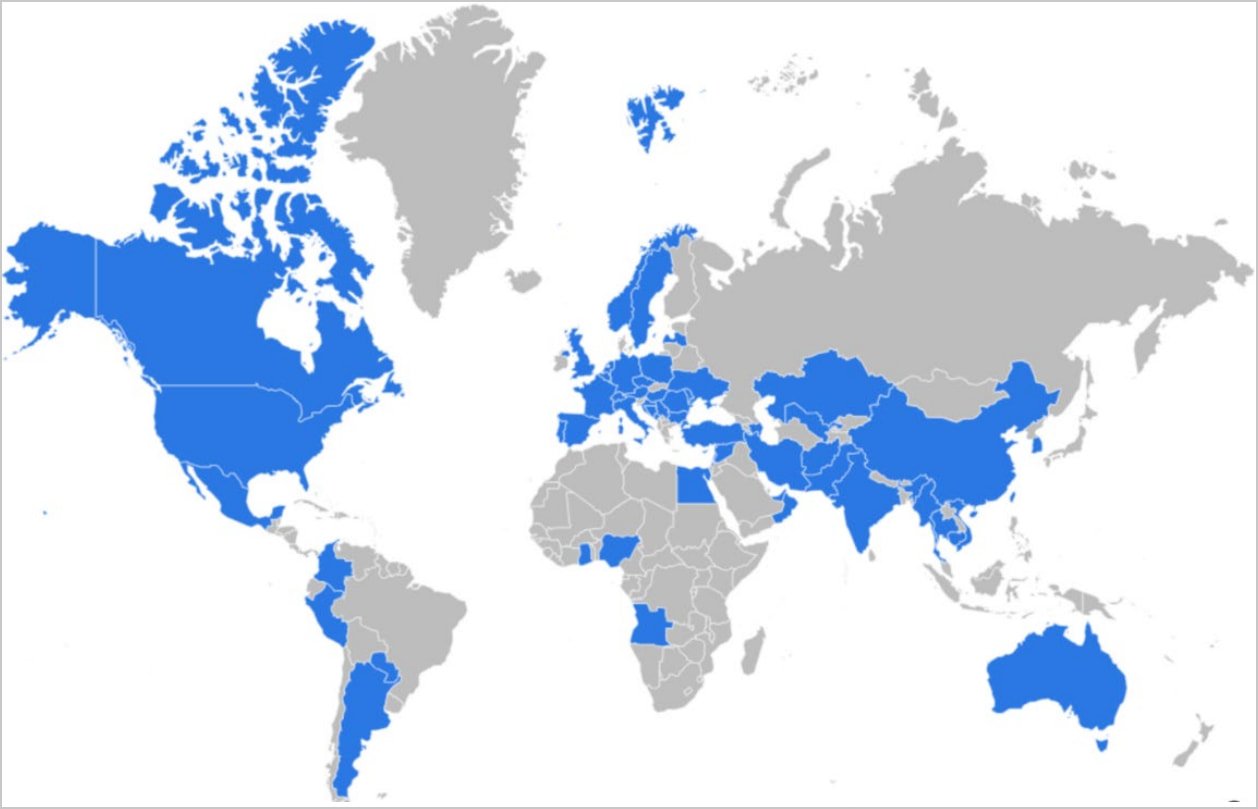
Microsoft’s earliest observations of the subgroup’s activity show opportunistic operations targeting Ukraine, Europe, Central and South Asia, and the Middle East, focusing on critical sectors.
Starting 2022, following Russia’s invasion of Ukraine, the subgroup intensified its operations against critical infrastructure supporting Ukraine, including government, military, transportation, and logistics sectors.
Their intrusions aimed at intelligence collection, operational disruptions, and wiper attacks aimed at corrupting data at the targeted systems.
“We assess that the subgroup has likely enabled at least three destructive cyberattacks in Ukraine since 2023,” mentions Microsoft regarding the subgroup’s specific activity.
By 2023, the subgroup’s targeting scope had broadened, conducting large-scale compromises across Europe, the United States, and the Middle East, and in 2024, it started focusing on the United States, United Kingdom, Canada, and Australia.
Initial access and post-compromise activity
The APT44 subgroup employs multiple techniques to compromise networks, including exploiting n-day vulnerabilities in internet-facing infrastructure, credential theft, and supply chain attacks.
Supply-chain attacks were particularly effective against organizations across Europe and Ukraine, where the hackers targeted regionally managed IT service providers and then accessed multiple clients.
Microsoft has observed network scans and subsequent exploitation attempts of the following vulnerabilities:
- CVE-2021-34473 (Microsoft Exchange)
- CVE-2022-41352 (Zimbra Collaboration Suite)
- CVE-2023-32315 (OpenFire)
- CVE-2023-42793 (JetBrains TeamCity)
- CVE-2023-23397 (Microsoft Outlook)
- CVE-2024-1709 (ConnectWise ScreenConnect)
- CVE-2023-48788 (Fortinet FortiClient EMS)
After exploiting the above vulnerabilities to obtain access, the hackers established persistence by deploying custom web shells like ‘LocalOlive’.
In 2024, the APT44 subgroup started to use legitimate IT remote management tools such as Atera Agent and Splashtop Remote Services to execute commands on compromised systems while posing as IT admins to evade detection.
Regarding the post-initial access activity, the threat actors use Procdump or the Windows registry to steal credentials, and Rclone, Chisel, and Plink for data exfiltration through covert network tunnels.
.jpg)
Researchers observed a novel technique in 2024 as the threat actor routed traffic through the Tor network “effectively cloaking all inbound connections to the affected asset and limiting exposures from both the actor and victim environment.”
Finally, the subgroup performs lateral movement to reach all the parts of the network it can, and modifies the infrastructure as required for its operations.
The modifications include DNS configuration manipulations, the creation of new services and scheduled tasks, and the configuration of backdoor access using OpenSSH with unique public keys.
Microsoft says that the Russian hacker subgroup has “near-global reach” and helps Seashell Blizzard expand its geographical targeting.
In the report published today, the researchers share hunting queries, indicators of compromise (IoCs), and YARA rules for defenders to catch this threat actor’s activity and stop it before .














