Hackers are launching attacks against Palo Alto Networks PAN-OS firewalls by exploiting a recently fixed vulnerability (CVE-2025-0108) that allows bypassing authentication.
The security issue received a high-severity score and impacts the PAN-OS management web interface and allows an unauthenticated attacker on the network to bypass authentication and invoke certain PHP scripts, potentially compromising integrity and confidentiality.
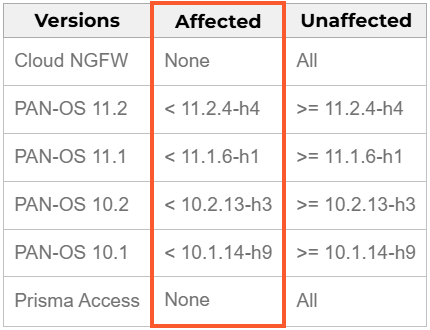
In a security bulletin on February 12, Palo Alto Networks urges admins to upgrade firewalls to the versions below to address the issue:
- 11.2.4-h4 or later
- 11.1.6-h1 or later
- 10.2.13-h3 or later
- 10.1.14-h9 or later
PAN-OS 11.0 is also impacted but the product reached the end of life (EoL) and Palo Alto Networks does not plan to release any fixes for it. Because of this, users are strongly recommended to upgrade to a supported release instead.
The vulnerability was discovered and reported to Palo Alto Networks by security researchers at Assetnote. They also published a write-up with complete exploitation details when the patch was released.
The researchers demonstrated how the flaw could be leveraged to extract sensitive system data, retrieve firewall configurations, or potentially manipulate certain settings within PAN-OS.
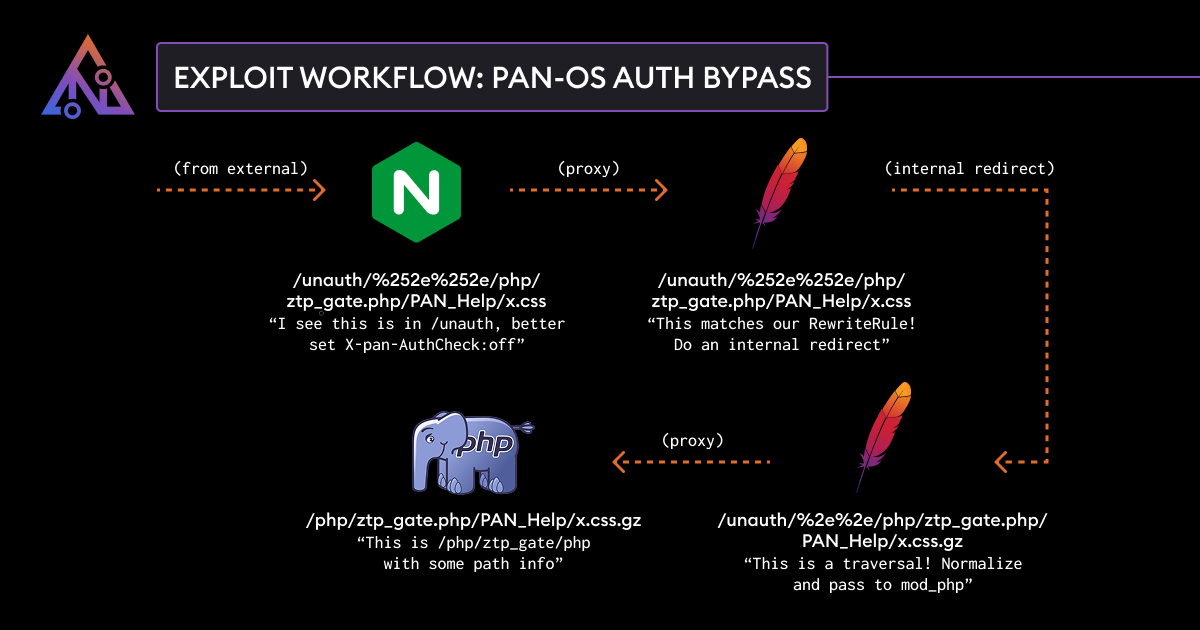
The exploit leverages a path confusion between Nginx and Apache in PAN-OS that allows bypassing authentication.
Attackers with network access to the management interface can leverage this to gather intelligence for further attacks or to weaken security defenses by modifying accessible settings.
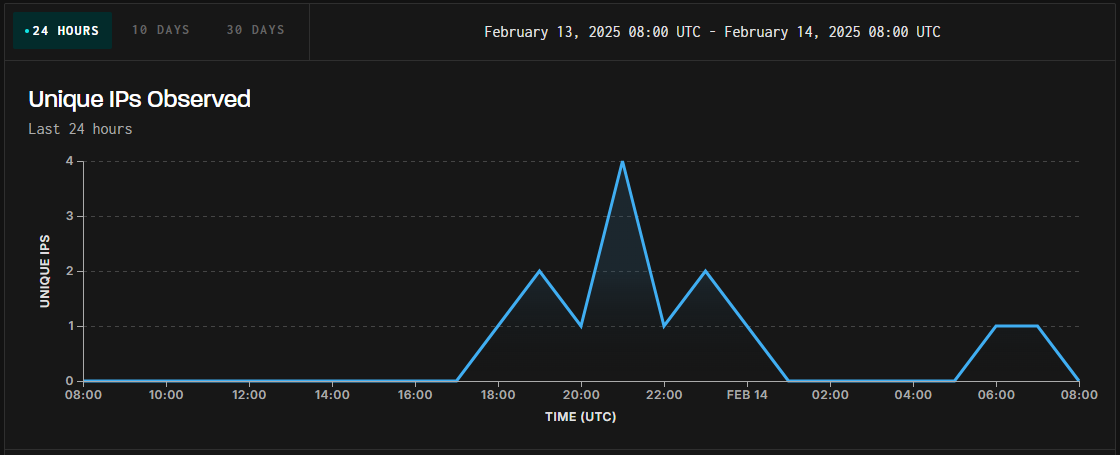
Threat monitoring platform GreyNoise logged exploitation attempts targeting unpatched PAN-OS firewalls.
The attacks started on February 13, at 17:00 UTC, and appear to originate from several IP addresses, potentially indicating exploitation efforts from distinct threat actors.
Regarding the exposure of vulnerable devices online, Macnica researcher Yutaka Sejiyama told BleepingComputer that there are currently over 4,400 PAN-OS devices exposing their management interface online.
To defend against the ongoing exploitation activity, which, considering that the PoC is public, is very likely to culminate in the following days, it is recommended to apply the available patches and restrict access to firewall management interfaces.
Update 2/18 – Palo Alto Networks sent BleepingComputer the below comment regarding the activity spotted in the wild.
“The security of our customers is our top priority. Palo Alto Networks has confirmed reports of active exploitation targeting a vulnerability (CVE-2025-0108) in the PAN-OS web management interface. This vulnerability, chained with other vulnerabilities like CVE-2024-9474, could allow unauthorized access to unpatched and unsecured firewalls.
We are urging all customers with internet-facing PAN-OS management interfaces to immediately apply the security updates released on February 12, 2025. Securing external-facing management interfaces is a fundamental security best practice, and we strongly encourage all organizations to review their configurations to minimize risk.
Detailed information and mitigation guidance are available in the CVE-2025-0108 security advisory: https://security.paloaltonetworks.com/CVE-2025-0108″














