Updated title to reflect thats these are not 64 million unique applicants, but rather applications on the job chatbot.
Cybersecurity researchers discovered a vulnerability in McHire, McDonald’s chatbot job application platform, that exposed the chats of more than 64 million job applications across the United States.
The flaw was discovered by security researchers Ian Carroll and Sam Curry, who found that the ChatBot’s admin panel utilized a test franchise that was protected by weak credentials of a login name “123456” and a password of “123456”.
McHire, powered by Paradox.ai and used by about 90% of McDonald’s franchisees, accepts job applications through a chatbot named Olivia. Applicants can submit names, email addresses, phone numbers, home addresses, and availability, and are required to complete a personality test as part of the job application process.
Once logged in, the researchers submitted a job application to the test franchise to see how the process worked.
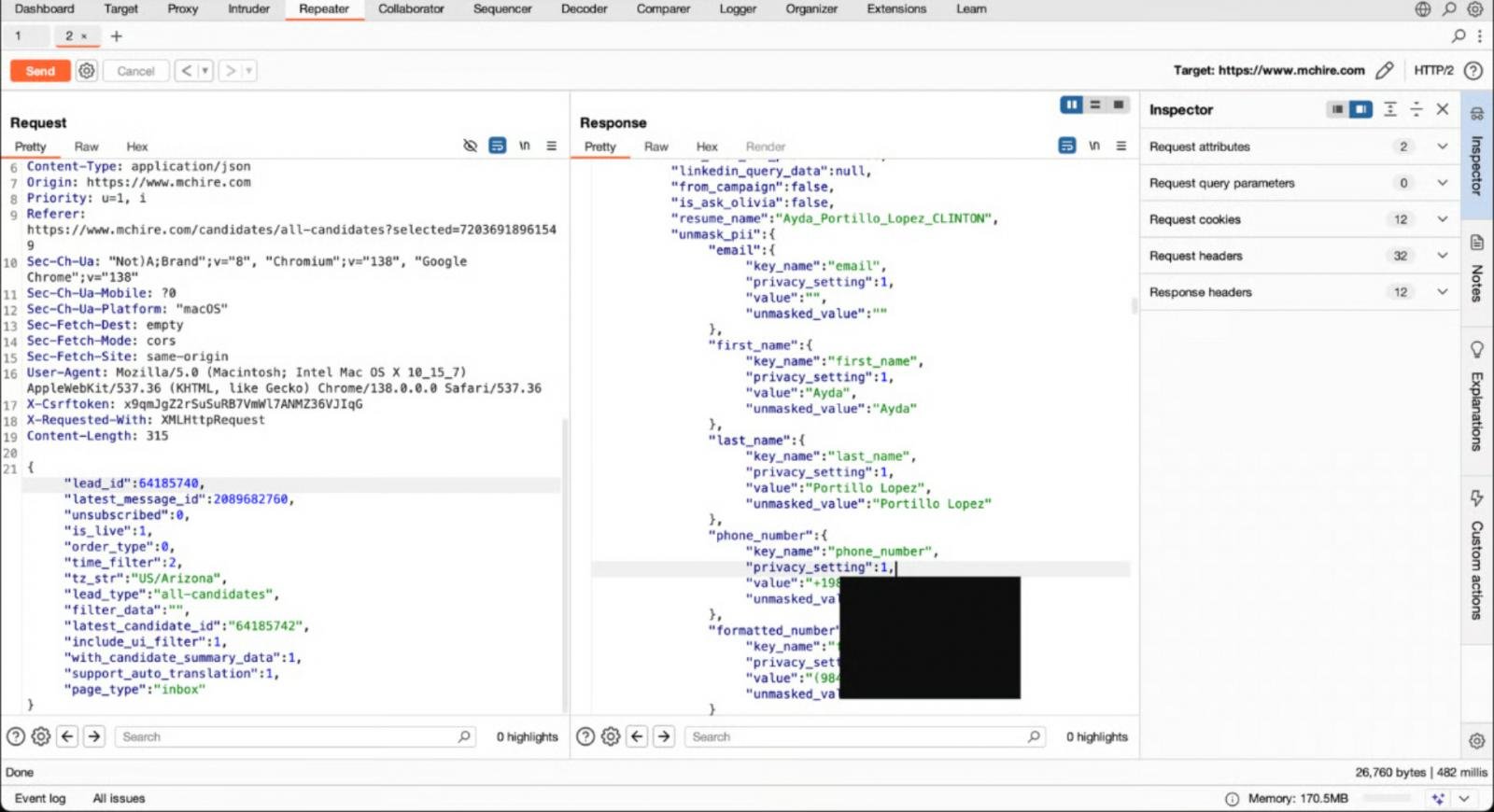
During this test, they noticed that HTTP requests were sent to an API endpoint at /api/lead/cem-xhr, which used a parameter lead_id, which in their case was 64,185,742.
The researchers found that by incrementing and decrementing the lead_id parameter, they were able to expose the full chat transcripts, session tokens, and personal data of real job applicants that previously applied on McHire.
This type of flaw is called an IDOR (Insecure Direct Object Reference) vulnerability, which is when an application exposes internal object identifiers, such as record numbers, without verifying whether the user is actually authorized to access the data.
“During a cursory security review of a few hours, we identified two serious issues: the McHire administration interface for restaurant owners accepted the default credentials 123456:123456, and an insecure direct object reference (IDOR) on an internal API allowed us to access any contacts and chats we wanted,” Carroll explained in a writeup about the flaw.
“Together they allowed us and anyone else with a McHire account and access to any inbox to retrieve the personal data of more than 64 million applicants.”
In this case, incrementing or decrementing a lead_id number in a request returned sensitive data belonging to other applicants, as the API failed to check if the user had access to the data.
The issue was reported to Paradox.ai and McDonald’s on June 30.
McDonald’s acknowledged the report within an hour, and the default admin credentials were disabled soon after.
“We’re disappointed by this unacceptable vulnerability from a third-party provider, Paradox.ai. As soon as we learned of the issue, we mandated Paradox.ai to remediate the issue immediately, and it was resolved on the same day it was reported to us,” McDonald’s told Wired in a statement about the research.
Paradox deployed a fix to address the IDOR flaw and confirmed that the vulnerability was mitigated. Paradox.ai has since stated that it is conducting a review of its systems to prevent similar big issues from recurring.
Paradox also told BleepingComputer that the information exposed would be any chatbot interaction, such as clicking on a button, even if no personal information was entered.
Update 7/11/25: Added information from Paradox.
Update 7/12/25: Changed title to applications to clarify that these are not unique applicants.

While cloud attacks may be growing more sophisticated, attackers still succeed with surprisingly simple techniques.
Drawing from Wiz’s detections across thousands of organizations, this report reveals 8 key techniques used by cloud-fluent threat actors.














